Experts Fear Crooks are Cracking Keys Stolen in LastPass Breach
Credit to Author: BrianKrebs| Date: Wed, 06 Sep 2023 00:21:07 +0000
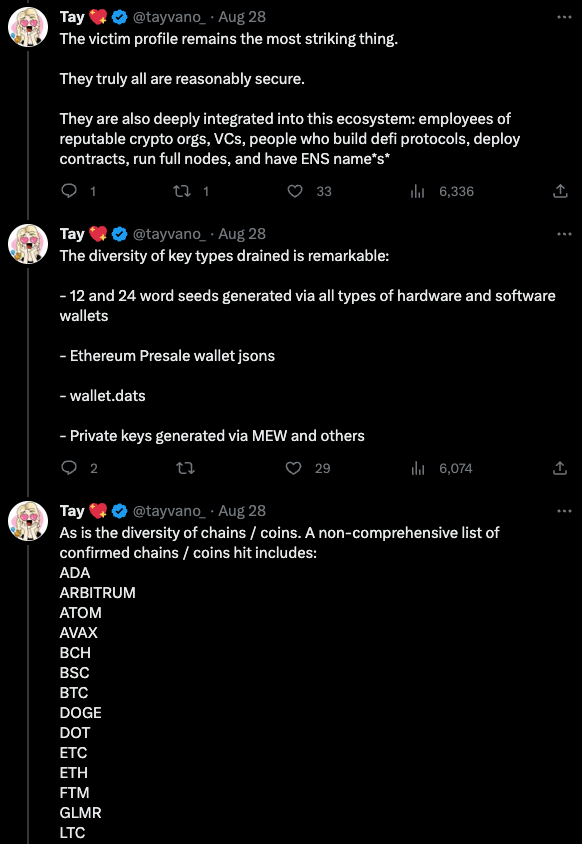
In November 2022, the password manager service LastPass disclosed a breach in which hackers stole password vaults containing both encrypted and plaintext data for more than 25 million users. Since then, a steady trickle of six-figure cryptocurrency heists targeting security-conscious people throughout the tech industry has led some security experts to conclude that crooks likely have succeeded at cracking open some of the stolen LastPass vaults.
Read more