Report: Recent 10x Increase in Cyberattacks on Ukraine
Credit to Author: BrianKrebs| Date: Fri, 11 Mar 2022 16:50:11 +0000
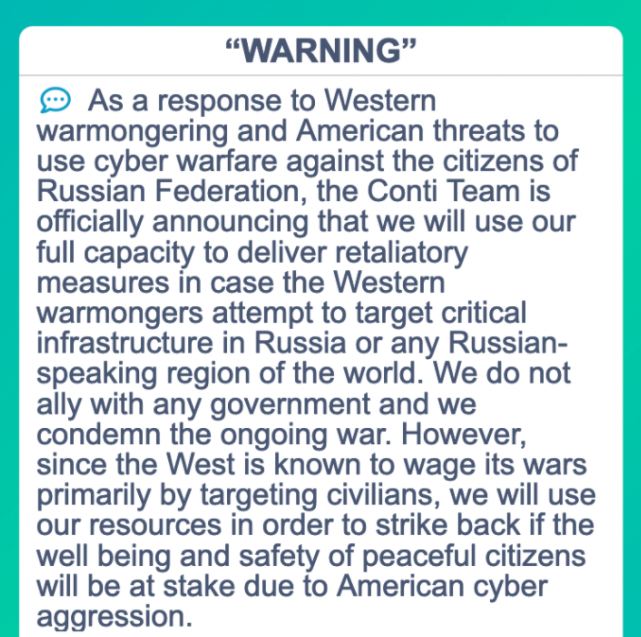
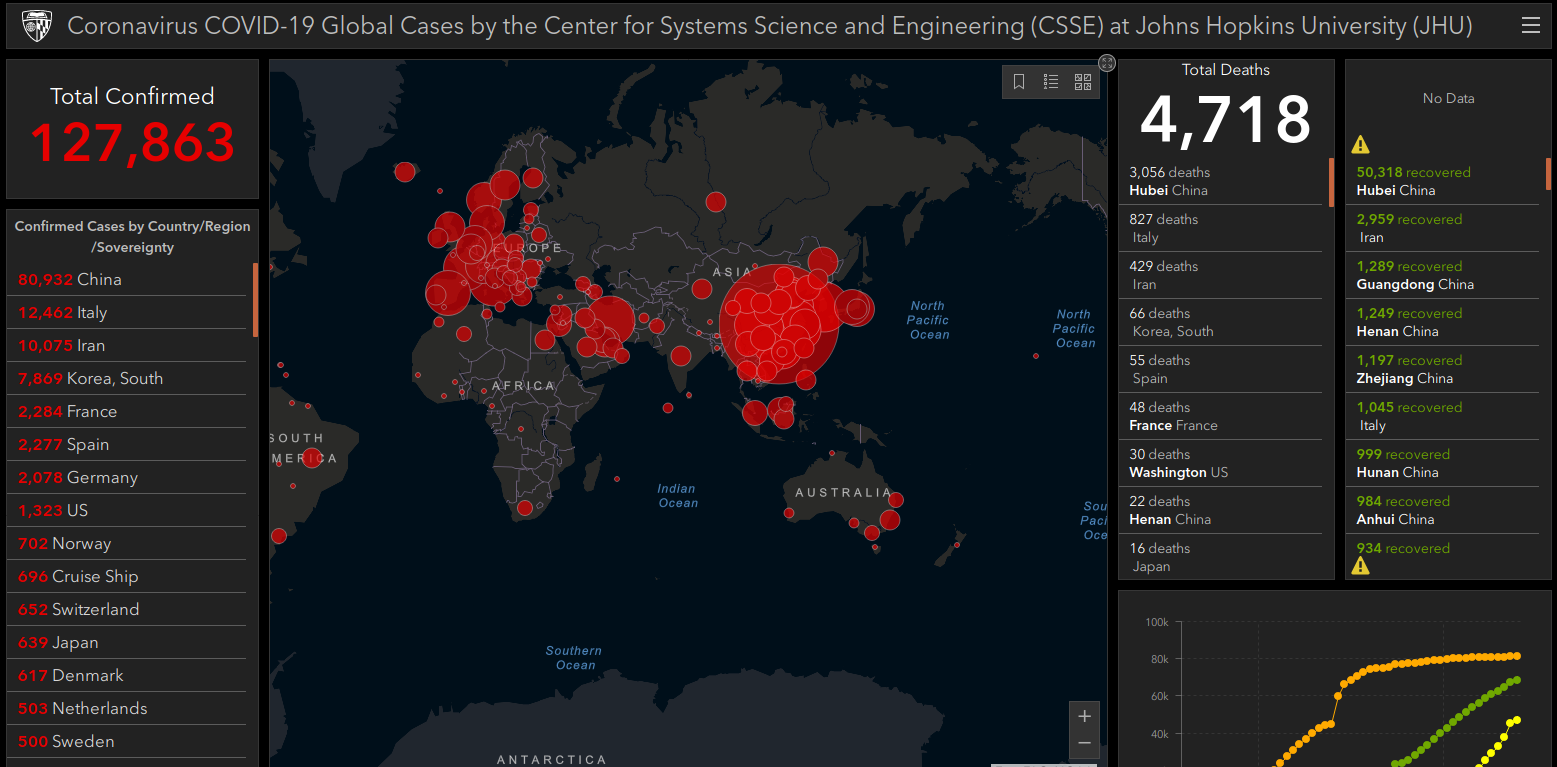
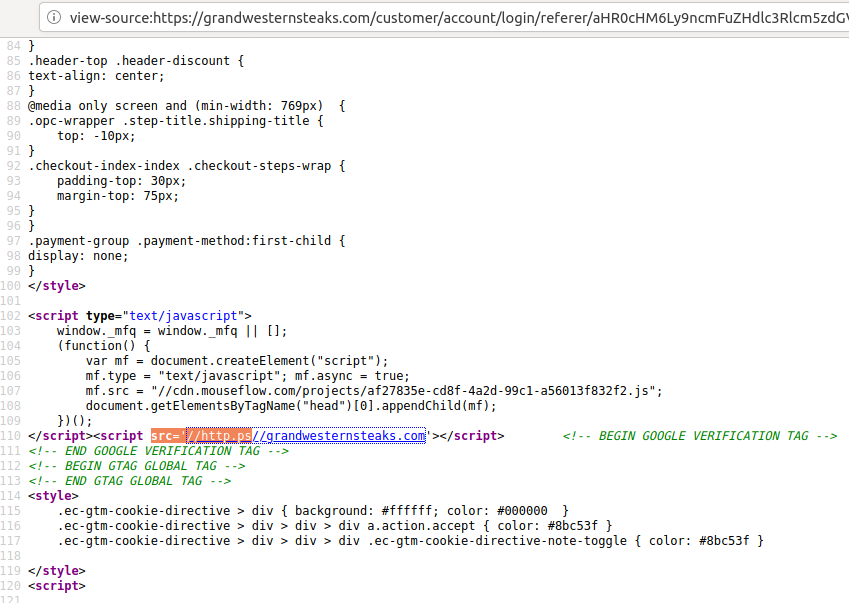
As their cities suffered more intense bombardment by Russian military forces this week, Ukrainian Internet users came under renewed cyberattacks, with one Internet company providing service there saying they blocked ten times the normal number of phishing and malware attacks targeting Ukrainians.
Read more