The Hidden Cost of Ransomware: Wholesale Password Theft
Credit to Author: BrianKrebs| Date: Mon, 06 Jan 2020 18:17:21 +0000
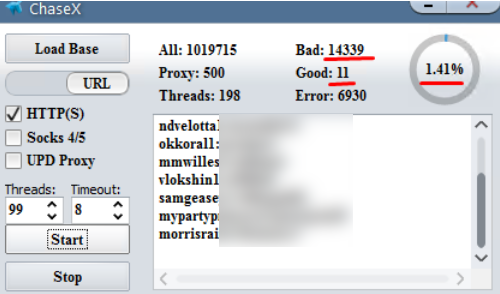
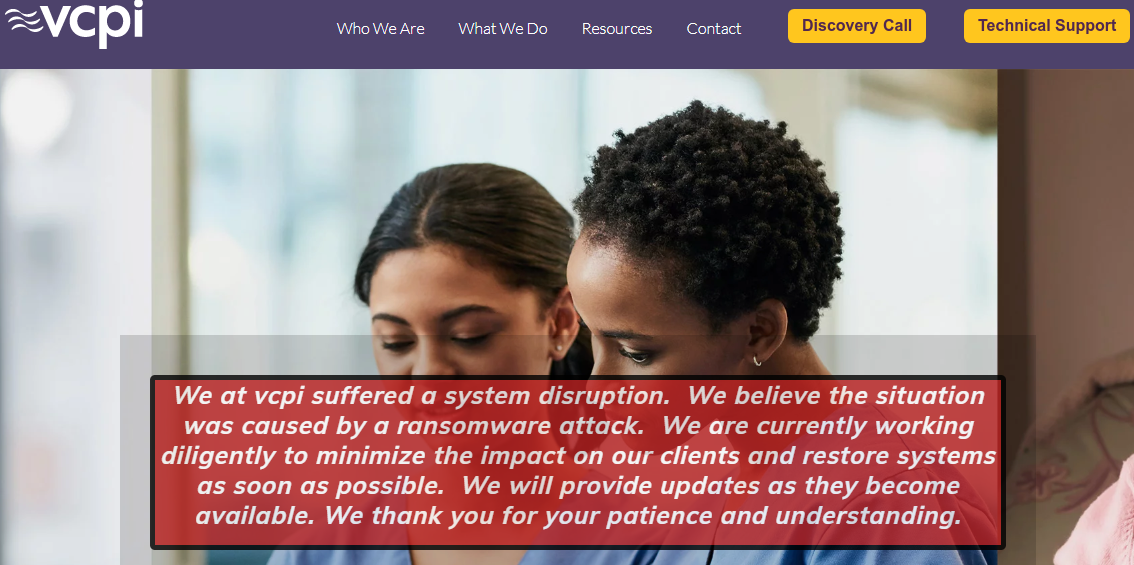
Organizations in the throes of cleaning up after a ransomware outbreak typically will change passwords for all user accounts that have access to any email systems, servers and desktop workstations within their network. But all too often, ransomware victims fail to grasp that the crooks behind these attacks can and frequently do siphon every single password stored on each infected endpoint. The result of this oversight may offer attackers a way back into the affected organization, access to financial and healthcare accounts, or — worse yet — key tools for attacking the victim’s various business partners and clients.
Read more