Crooked Cops, Stolen Laptops & the Ghost of UGNazi
Credit to Author: BrianKrebs| Date: Mon, 30 Sep 2024 21:33:10 +0000
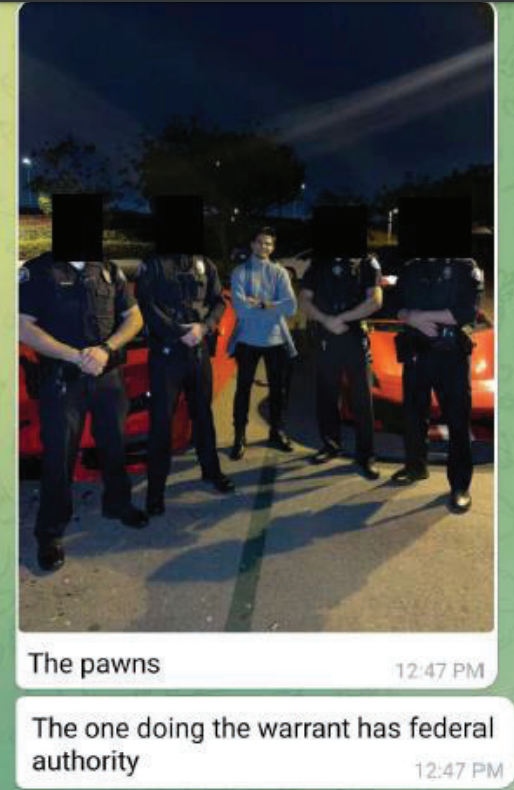
A California man accused of failing to pay taxes on tens of millions of dollars allegedly earned from cybercrime also paid local police officers hundreds of thousands of dollars to help him extort, intimidate and silence rivals and former business partners, a new indictment charges. KrebsOnSecurity has learned that many of the man’s alleged targets were members of UGNazi, a hacker group behind multiple high-profile breaches and cyberattacks back in 2012.
Read more


