Ticketmaster confirms customer data breach
Live Nation Entertainment has confirmed what everyone has been speculating on for the last week: Ticketmaster has suffered a data breach.
In a filing with the SEC, Live Nation said on May 20th it identified “unauthorized activity within a third-party cloud database environment containing Company data (primarily from its Ticketmaster L.L.C. subsidiary)” and launched an investigation.
The third party it refers to is likely Snowflake, a cloud company used by thousands of companies to store, manage, and analyze large volumes of data. Yesterday, May 31st, Snowflake said it had “recently observed and are investigating an increase in cyber threat activity” targeting some of its customers’ accounts. It didn’t mention which customers.
In the SEC filing, Live Nation also said:
On May 27, 2024, a criminal threat actor offered what it alleged to be Company user data for sale via the dark web. We are working to mitigate risk to our users and the Company, and have notified and are cooperating with law enforcement. As appropriate, we are also notifying regulatory authorities and users with respect to unauthorized access to personal information.
The user data likely refers to the sales ad for 560 million customers’ data that was posted online earlier this week by a group calling themselves ShinyHunters. The data was advertised for $500,000 and says it includes customer names, addresses, emails, credit card details, order information, and more.
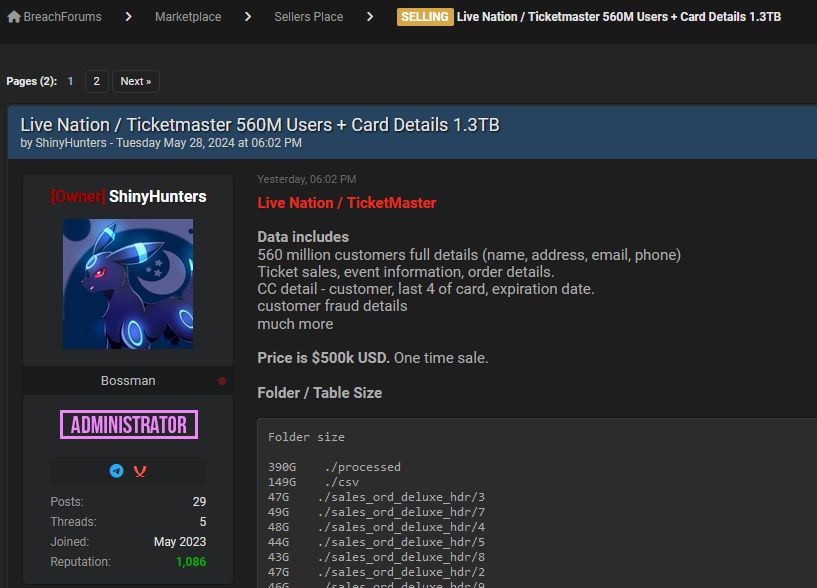
Bleeping Computer says it spoke to ShinyHunters who said they already had interested buyers, and believed one of the buyers that approached them was Ticketmaster itself.
Ticketmaster says it has begun notifying its users of the breach. We are likely to hear more in the coming days, and will update you as we do.
For now, Ticketmaster users should keep an eye on their credit and bank accounts for an unauthorized transactions and follow our general data breach tips below.
Protecting yourself after a data breach
There are some actions you can take if you are, or suspect you may have been, the victim of a data breach.
- Check the vendor’s advice. Every breach is different, so check with the vendor to find out what’s happened, and follow any specific advice they offer.
- Change your password. You can make a stolen password useless to thieves by changing it. Choose a strong password that you don’t use for anything else. Better yet, let a password manager choose one for you.
- Enable two-factor authentication (2FA). If you can, use a FIDO2-compliant hardware key, laptop or phone as your second factor. Some forms of two-factor authentication (2FA) can be phished just as easily as a password. 2FA that relies on a FIDO2 device can’t be phished.
- Watch out for fake vendors. The thieves may contact you posing as the vendor. Check the vendor website to see if they are contacting victims, and verify any contacts using a different communication channel.
- Take your time. Phishing attacks often impersonate people or brands you know, and use themes that require urgent attention, such as missed deliveries, account suspensions, and security alerts.
- Consider not storing your card details. It’s definitely more convenient to get sites to remember your card details for you, but we highly recommend not storing that information on websites.
- Set up identity monitoring. Identity monitoring alerts you if your personal information is found being traded illegally online, and helps you recover after.
Scan for your exposed personal data
While the Ticketmaster data is yet to be published in full, it’s likely you’ve had other personal information exposed online in previous data breaches. You can check what personal information of yours has been exposed with our Digital Footprint portal. Just enter your email address (it’s best to submit the one you most frequently use) to our free Digital Footprint scan and we’ll give you a report.