Foundations of Flow—secure and compliant automation, part 2
Credit to Author: Todd VanderArk| Date: Wed, 11 Sep 2019 16:00:28 +0000
In part 1 of this series, we introduced you to Microsoft Flow, a powerful automation service already being used by many organizations across the world. Flow is designed to empower citizen developers while featuring capabilities sought for by professional developers. Flow is also a foundational element of the Microsoft Power Platform announced earlier this year.
More organizations are seeking automation solutions and there will be many options. As security professionals, you’ll have to recommend the service offering all the benefits of automation, while ensuring the organization remains secure and compliant. Flow is natively integrated with best-in-class authentication services, offers powerful data loss prevention and an enhanced IT experience ranging from broad visibility and control to automating IT functions, and is built on rigorous privacy and compliance standards. We’re confident that Flow will be the right choice for your organization, so let’s get started on showing you why.
Prioritized security for your users and data
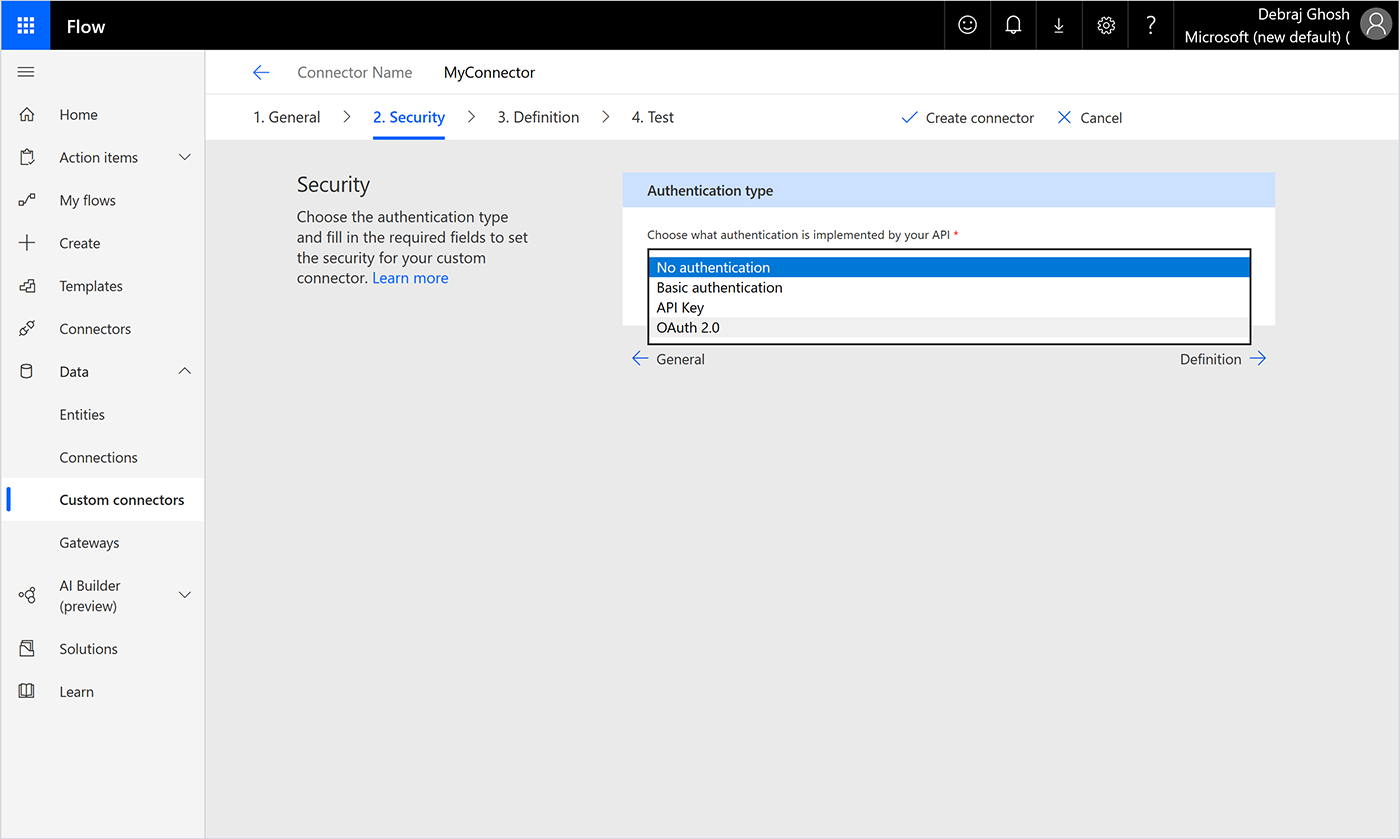
Flow is seamlessly integrated with Azure Active Directory (Azure AD), one of the world’s most sophisticated, comprehensive, and secure identity and access management services. Azure AD helps secure the citizen developer by protecting against identity compromise, gives the IT admin/pro visibility and control, and offers additional security capabilities for the pro developer. Azure AD helps support the least privilege strategy, which we recommend for Flow users. Azure AD also follows a federated model, so organizations not directly using the service are still secure. Since authentication to Flow is via Azure AD, admins using its premium features can create conditional access policies which restrict user access to only the apps and data relevant for their role. Flow’s integration with Azure AD also enhances security for more experienced developers who can register applications with the service and leverage multiple authentication protocols, including the OAuth2 authorization framework to enable their code to access platform APIs (Figure 1). This access protection can also be extended to external users.
Figure 1. Choosing authentication framework for custom Flow connector.
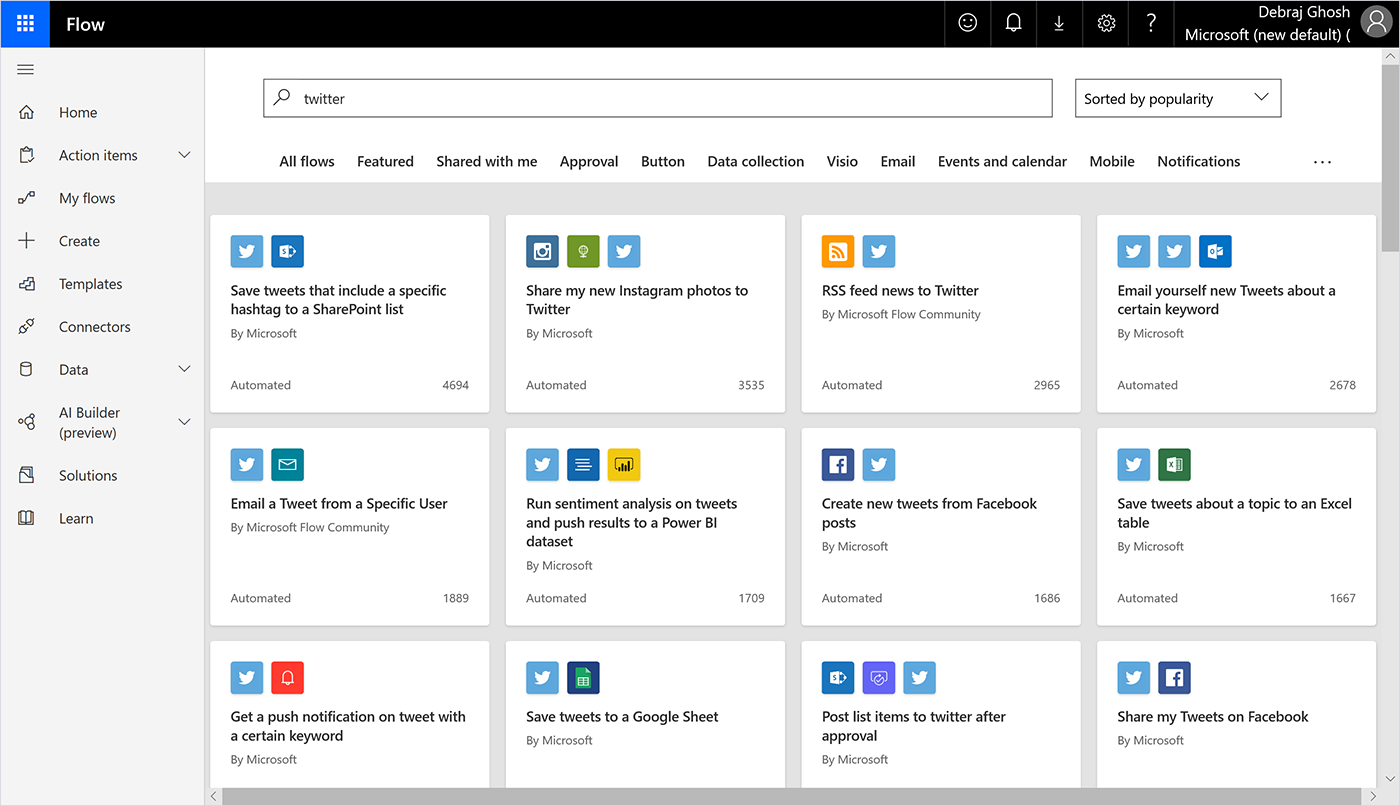
To experience the full benefits of automation and unlock the potential of an organization’s data, Flow offers 270+ connectors to services, including third-party services. Some connectors are even built for social media sites, such as Twitter (Figure 2). With so many integrations, there’s always the threat of data leakage or compromise. Imagine the scenario where a user mistakenly tweets sensitive data. To prevent these types of scenarios, Flow is supported by the Microsoft Data Loss Prevention (DLP) service.
Figure 2. Pre-built Flow templates offering automation between Twitter and several other applications.
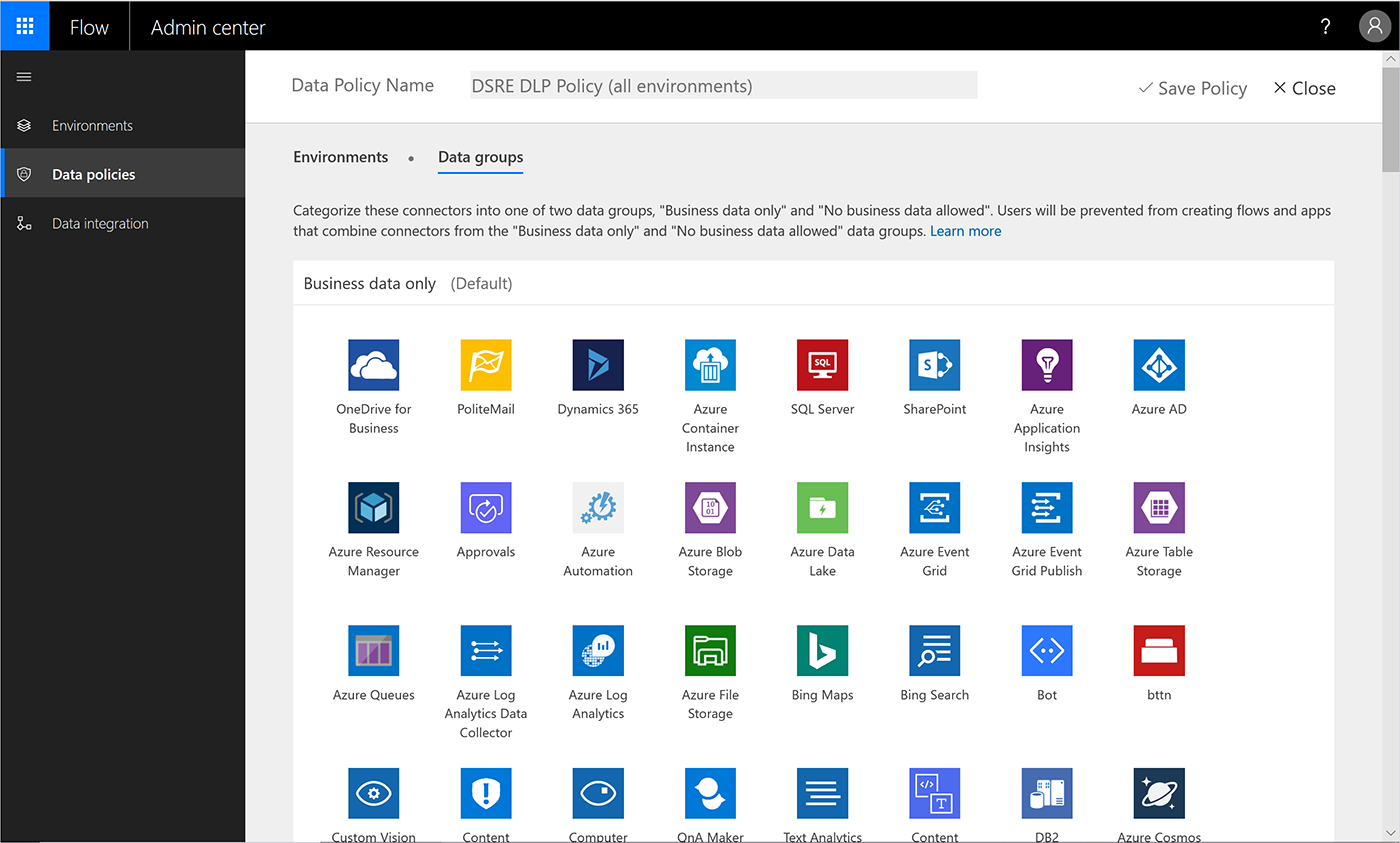
Microsoft DLP protects data from being exposed and DLP polices can be easily created by administrators. DLP policies can be customized at the user, environment, or tenant level to ensure security is maintained without impact to productivity. These policies enforce rules of what connectors can be used together by classifying connectors as either “Business Data Only” or “No Business Data Allowed” (Figure 3). A connector can only be used with other connectors within its group. For example, a connector in the Business Data Only group can only be used with other connectors from that group. The default setting for all connectors is No Business Data Allowed.
Importantly, all data used by Flow is also encrypted during transit using HTTPS. As a security leader, you can feel reassured that Flow is designed to ensure your data is secured both at rest and in transit with strict enforcement. To learn more about strategies to create DLP polices for Flow connectors, check out our white paper.
Figure 3. Flow Admin center where you can create DLP policies to protect your sensitive while benefiting from the powerful automation capabilities offered with Flow.
Enhancing management of the IT environment
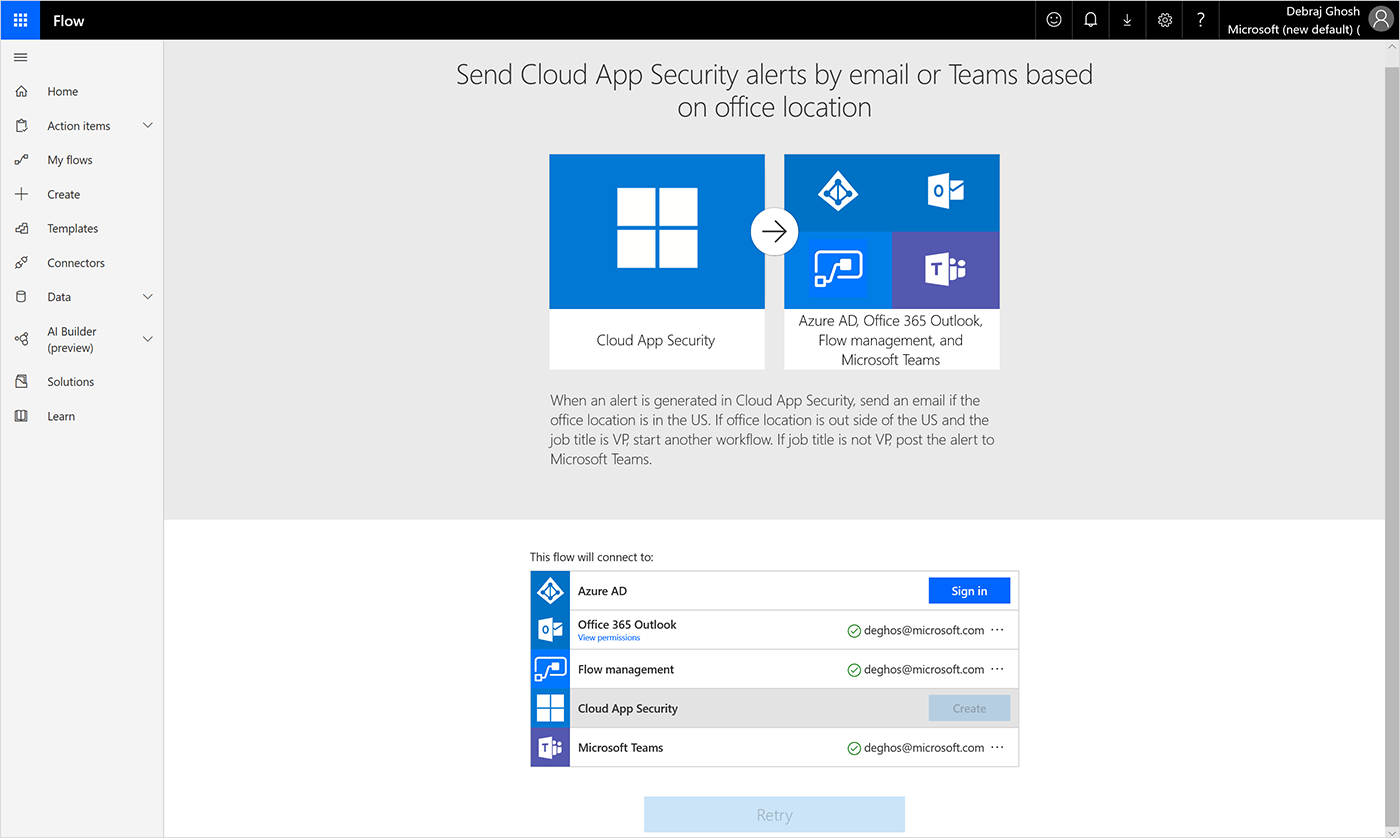
Flow includes the Flow management connector, which enables admins to automate several IT tasks. The management connecter offers 19 possible actions that can be automated—from creating and deleting Flows to more complex actions, such as modifying the owner of a Flow. The Flow management connector is versatile and can be combined with other connectors to automate several admin tasks, enhancing the efficiency of IT teams. For example, security admins can create a Flow combining the management connector with Azure AD, Microsoft Cloud App Security, Outlook, and Teams to quickly send automatic notifications via email or Teams anytime Cloud App Security generates an alert on suspicious activity (Figure 4). Other use cases could include a notification when a new app is created, automatically updating user permissions based on role changes, or tracking when custom connectors are created in your environment.
Figure 4. Flow template using the management connecter, Azure AD, Cloud App Security, Outlook, and Teams.
Visibility of activity logs
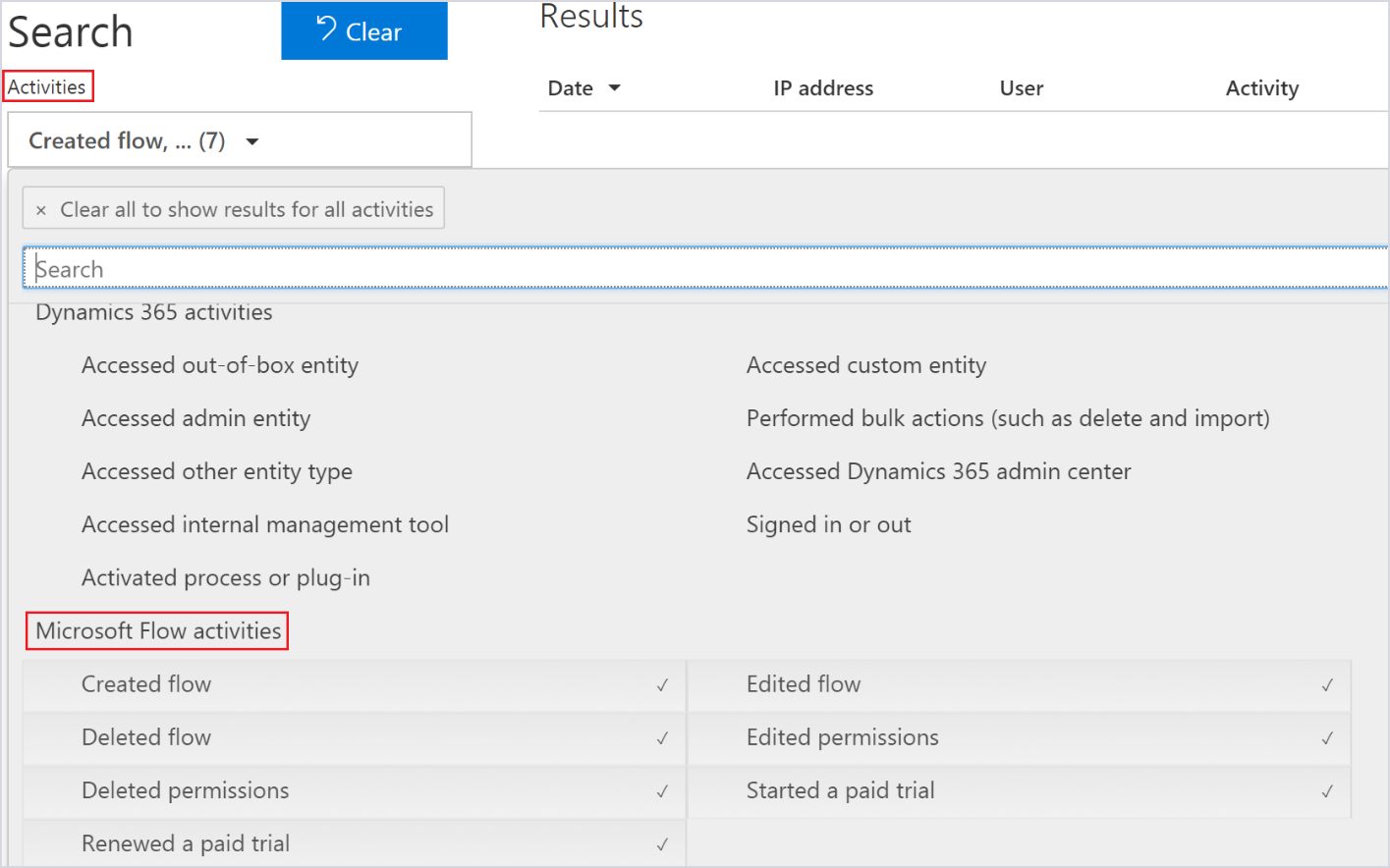
Many of Flow’s current users are also Office 365 users. As such, Flow event logs are available in the Office 365 Security & Compliance Center. By surfacing activity logs in the Security & Compliance Center, admins gain visibility into which users are creating Flows, if Flows are being shared, as well as which connectors are being used (Figure 5). The activity data is retained for 90 days and can be easily exported in CSV format for further analysis. The event logs surface in the Security & Compliance Center within 90 minutes of the event taking place. Admins also gain insight on which users are using paid versus trial licenses in the Security & Compliance Center.
Figure 5. Microsoft Flow activities accessed through the Office 365 Security & Compliance Center.
Strict on data privacy and regulatory requirements
Flow adheres to Microsoft’s strict standards of privacy and protection of customer data. These policies prohibit customer data from being mined for marketing or advertising. Microsoft personnel and subcontractors are also restricted from accessing customer data and we carefully define requirements for responding to government requests for customer data. Microsoft also complies with international data protection laws regarding transfers of customer data across borders.
Microsoft Flow is also certified for many global, government, industrial, and regional compliance regulations. You can see the full list of Microsoft certifications, while Table 1 summarizes the certifications specifically covered by Flow.
| Global | Government | Industry | Regional |
| CSA-STAR-Attestation | UK G-Cloud | HIPAA/HITECH | EU-Model-Clauses |
| CSA-Star-Certification | HITRUST | ||
| ISO 27001 | PCI DSS | ||
| ISO 27018 | |||
| ISO 9001 |
Table 1. Flow’s existing certifications.
Let Flow enhance your digital transformation
Let your organization start benefiting from one of the most powerful and secure automation services available on the market. Watch the video and follow the instructions to get started with Flow. Be sure to join the growing Flow community and participate in discussions, provide insights, and even influence product roadmap. Also follow the Flow blog to get news on the latest Flow updates and read our white paper on best practices for deploying Flow in your organization. Be sure to check out part 1, where we provide a quick intro into Flow and dive into its best-in-class, secure infrastructure.
Additional resources
- Sign up for Microsoft Flow—just click or tap Sign up free in the upper-right corner.
- Visit the Flow community to connect with peers, share ideas, and learn from experts.
- Read the Flow blog to get the latest news.
- Read Administering a PowerApps Enterprise Deployment Technical white paper.
- Watch the Microsoft Flow: Getting Started video.
- Read Foundations of Microsoft Flow—secure and compliant automation, part 1.
The post Foundations of Flow—secure and compliant automation, part 2 appeared first on Microsoft Security.